HCriffin plays an important role in security monitoring of organization, being easy to deploy Out-of-band model without affecting the infrastructure.
· Early alert of APT attacks on the network layer through IOCs, intrusion signatures
· Detecting attacks and network security threats based on patterns, with more than 25000 rules that updated, periodically optimized
· Real-time detection of anomalies, exploit attacks, violations, anomalous services, C&C connections in the network
· Collect and extract packets, PCAP to support in-depth investigation of information security incidents
· Scan sensitive files in network flow
· Store full content network data in the form of PCAP files for analysis and reconstruction of network connections to investigate
· Allows searching on HCriffin network activities: session, SMB, HTTP, DNS, SSH, threat hunting and tracing in the network
· Centralized administration and allows integration of security monitoring systems such as SIEM, SOAR. In addition, the integration of Threat Intelligence systems and sources helps HCriffin achieve high efficiency in early alert.
Network layer attack detection
HCriffin detects advanced threats with industry-leading application recognition and application-level data analysis. HCriffin provides an attack detection rule set management interface, defaults to more than 25000 rules and automatically updates new rule sets, allowing to detect many different groups of malicious behavior on the network layer, which are continuously added. and allows customization to detect the latest attack signatures.
• Scanning network segment, network port
• Detect malicious code connection, C&C connection, botnet
• Detect known exploit code being executed
• Detect web application attack, application vulnerability exploitation
• Detect abnormal login behavior
• Detect APT attack
• Detect intrusions with continuously updated IOCs
Support to ensure compliance and audit
HCriffin inspects and analyzes packets to help detect operational issues, policy violations, and compliance
· Detecting violations of using online chat software, using torrent download software...
· Detect unauthorized protocols, abnormal network port usage protocols
· Detects out-of-hours logins, invalid sensitive file transfers
· Detects weak, outdated protocols used that expose passwords and sensitive information
· Detect some network performance bottlenecks
Built-in Sandbox
The built-in sandbox aims to enhance the system's ability to detect malware infections, malicious file transfers, and network hacking tools, especially unknown malwares. HCriffin allows integration with an automated malware analysis system that enhances monitoring, especially for APT attacks, using new types of malwares, requiring a dynamic analyzer.
HCriffin performs a dissection and sends suspicious files or specified file types to the sandbox system for inspection and analysis, based on the captured data stream:
· Keeping payloads, binary files suspected of malicious code
· Perform dissection, send suspicious files to sandbox analysis
· Behavioral alerts based on sandbox analysis results
In-depth analysis and investigation
HCriffin assists monitoring team to do in-depth investigation, review and analysis of network incidents, as well as threat hunting
· Hunt connections for a signal of a cyber attack
· Hunt connections related to an IP address, computer in the network
· Support to reconstruction connections and queries in the network in the form of PCAP to serve the investigation and analysis of deep transfer
· Investigate network traffic anomalies by protocol
· Baseline network behavior of the system
· Enables powerful free search to drill down into network flows and critical packet data and streamline the investigation
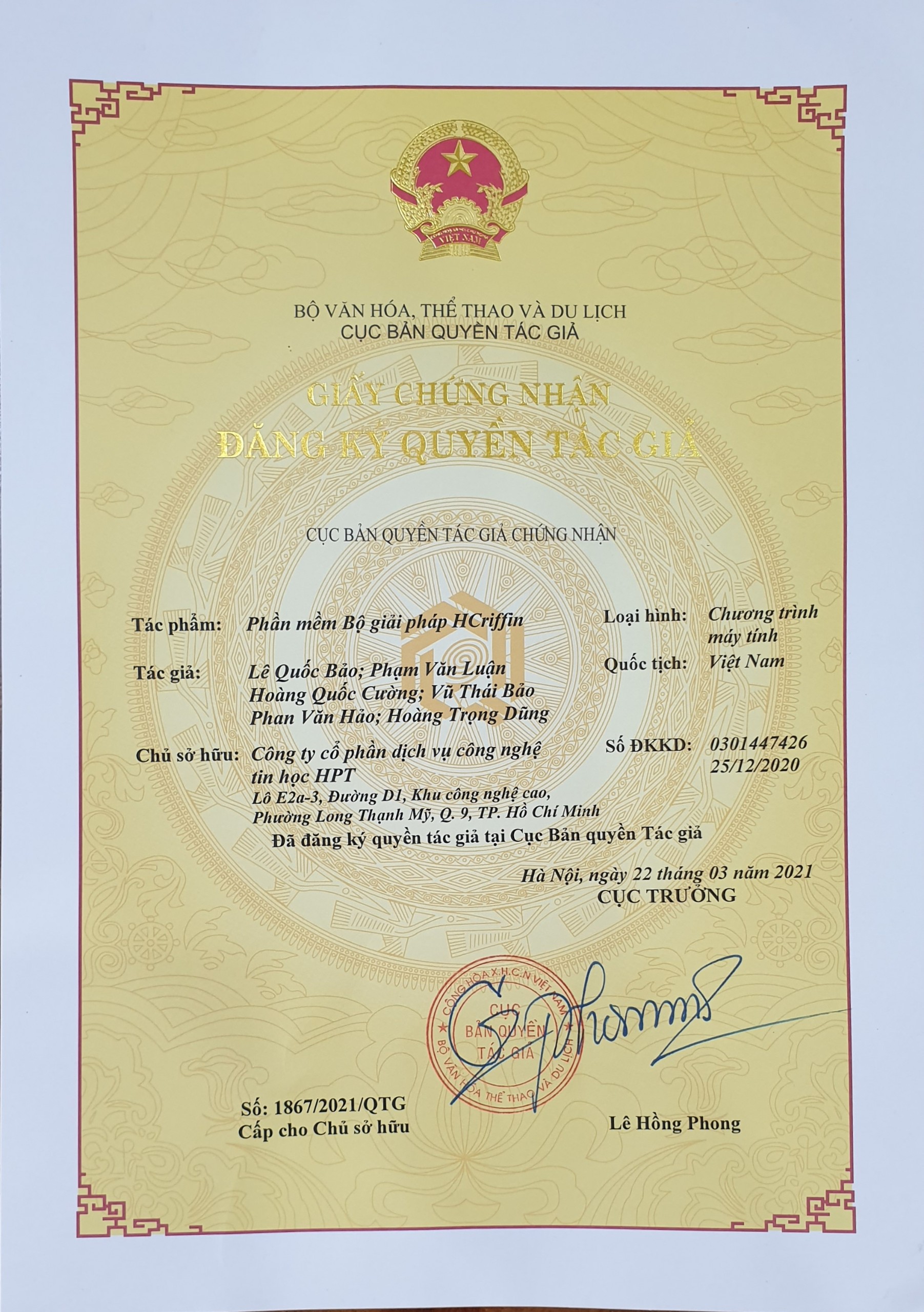
Product is certified by Copyright Department